Blog, TrapezoidFIVE, firmware, All, cyberattacks, cybersecurity, Trapezoid
The Problem with Firmware
Guest blog | José González, CEO – Trapezoid, Inc.
Would you secure your windows and doors but leave the basement door wide open?
Well, that’s what organizations are doing with firmware.
Simply put, firmware is the unmonitored and unprotected layer at the bottom of the computer code stack. While existing security tools have a done great job focusing on application and operating system levels, firmware has been overlooked. Exacerbating the problem: Firmware has the most permissions of any code on your system, which increases the impact of an attack. Firmware is everywhere; from the largest data center to the smallest networked LED light bulb. It is the most powerful code on any system because it controls how other code on a device interacts with its hardware (keyboard, screen, storage, network). Compromised firmware can corrupt or steal data, spy on your environment or even destroy the system it is controlling.How firmware gets compromised
Compromised firmware takes two forms: bad actors installing malware posing as legitimate firmware on systems, or manufacturers discovering vulnerabilities in their firmware and publishing updates. Compromised firmware can shut down your operations by taking out your critical infrastructure. Unmonitored firmware exposes enterprises to an unacceptable level of risk for devastating financial harm to businesses and life-threatening consequences for consumers. You don’t have to look far for examples of firmware attacks and breaches – they’re in the news daily. From devastating attacks on global routers and national powergrids, to vulnerabilities in medical devices, government and business networks, home computers and devices, smartphones and handheld devices…virtually anything that is part of the “ Internet of things”. Because this is a very real risk, all the major cybersecurity and compliance frameworks include controls dictating best practices around firmware patch management, and many include controls for continuous monitoring of firmware integrity. Why do so many organizations leave firmware out of their cybersecurity program?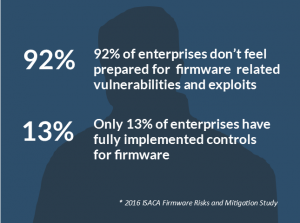
The next generation of firmware protection is here
T-5 closes the “basement door” while providing you visibility into an area previously uninspected. It continuously monitors and alerts on changes in firmware integrity, quickly identifies systems that need patching – and provides threat updates for you to stay on top of newly discovered vulnerabilities. T-5 acts like a firmware DVR to forensically prove to auditors the state of the integrity of your infrastructure from the time T-5 begins monitoring. Because it integrates with existing security tools, T-5 brings visibility of the firmware space, which those tools currently cannot see. Moreover, T-5 meets cyber security compliance controls such as HIPAA, HITRUST, NIST CSF, FISMA/FedRAMP, PCI-DSS, ISO/IEC 20001 and the FFIEC Cybersecurity Assessment Tool. One thing is clear, the proliferation of the connected devices is not slowing down, and neither are hackers. T-5 is the advanced level of firmware integrity protection you need for all your assets that support your operations, systems, information, finances, revenue streams and people.For more information on firmware risks and Trapezoid5, visit Trapezoid.com.
